Download: AntiSpam Mailto v1.0.5 (91 KB)
AntiSpam Mailto (previously named Email Address Encryptor) is an email address encryptor / obfuscator program. It will encrypt the 'mailto:' HTML code that contains your clickable email address with JavaScript. This allows you to publish a fully functional email address link on your website that is invisible to the majority of spammer's harvesters.
Spammers use bots (called harvesters or spiders) that continually download webpages, searching for email addresses. They will later send unsolicited email (spam) to this collection of addresses. If your email address exists on a webpage somewhere, it is pretty much guaranteed that some spammer knows about it. AntiSpam Mailto will encrypt / obfuscate your email address into JavaScript code making it extremely difficult for these bots to find it. Only the most complex bots -- ones that can parse complex JavaScript code -- will be able to 'see' it.
As some bots can parse JavaScript, this is not the end-all solution to spam. This program merely reduces the chances of your email being found by spammers. It is recommended that you use this program in conjunction with an email spam filter.
AntiSpam Mailto exists to help reduce spam for these people who wish to have a fully workable email address link on their website, and is meant to be a replacement for the following flawed ways of hiding your email address from harvesters:
-
Some webpages show a fake email address such as: someone AT example DOT com or someoneREMOVE@example.MEcom. This is annoying to the surfer who must modify the email address to make it usable. Websites that do this place the onus of fighting spam on the surfer. The attitude "the surfer will figure it out if she really wants to email me" is ignorant as you will find your inbox void of not only spam, but of legitimate email from visitors that you do not want to miss. Also, some bots will harvest this type of encryption, anyway -- especially the inclusion of AT and DOT, since it is so common, and so easily decryptable.
-
Some webpages show an image of the email address:
 A bot would have to use OCR (optical character recognition) to extract the email address from this image. This is unlikely to happen, given the amount of bandwidth and CPU power that would be required to scan every small image that may happen to contain an email address. Therefore, this is excellent for fighting spam. The real problem lies in the forcing of addition work by the surfer to type the entire email address manually, which is annoying and prone to error.
A bot would have to use OCR (optical character recognition) to extract the email address from this image. This is unlikely to happen, given the amount of bandwidth and CPU power that would be required to scan every small image that may happen to contain an email address. Therefore, this is excellent for fighting spam. The real problem lies in the forcing of addition work by the surfer to type the entire email address manually, which is annoying and prone to error.
-
Some webpages use basic HTML encoding, such as using
@to show the at-sign (@). Some will go further, and use such encoding for every letter and symbol within the email address. For example, the following is the encryption ofsomeone@example.com:
someone@ex ample.com
You may think, "Aha! Decrypt that!" But, while the process looks complicated to a human, it is almost as easy as reading regular text to a bot. Any bot that is programmed to decrypt the@code into the at (@) sign will also be able to decrypt each of these characters. It is easy because each number in the sequence corresponds exactly to a single character, such as:
ais equivalent to 'a'
bis equivalent to 'b'
cis equivalent to 'c'
...
xis equivalent to 'x'
yis equivalent to 'y'
zis equivalent to 'z'
Using this, you can easily decrypt this by hand -- thus, surely a havester can. It does not require parsing programming code; it can run through the numbers and convert them as it downloads the webpage.
- Some companies will use a web form (PHP sendmail) to allow contact. To many, this appears to be the ultimate solution. But, not so fast... This forces the surfer to use the company's clunky web interface for sending them an email, instead of allowing them to use their own email client, which they are familiar with. The web form does not allow a copy of the email to be saved within the surfer's regular email client. The surfer cannot even be entirely sure if the web form even works or not, as the surfer will not get a bounce message if it does not work properly. Many companies get carried away with their power to regulate such forms, imposing restrictions which force the surfer to enter their full name, phone number, best time to be called, etc. Failure to do so will result in a refusal to send the email. The surfer may not wish to reveal such information. Some web forms have bugs that make it refuse to work under certain curcumstances that the programmers are not aware of. A web form is a company's solution to their spam problem, which does the trick, but they are moving the burden to their customers. This is not appropriate.
Notes:
JavaScript is client-side, not server-side, so this will not bog down your host. It is the surfer's machine that parses it. However, the size of the webpage will be slightly increased when using this program, since the JavaScript is more bulky than a regular email link. It is recommended to place the JavaScript in a .js file that all other HTML files can refer to. The browser will download this .js file only once, no matter how many pages refer to it for this same email address.
Approximately 2% of all surfers have JavaScript disabled. On a browser without JavaScript enabled, the JavaScript code will be ignored, and the browser will run the code within the <noscript> tags. By default, the code created by AntiSpam Mailto will not show the email address, since a harvester would be able to grab it. Instead, it gives a 'convenient' link to a Google search on how to enable JavaScript, so the email address can be viewed, if desired. The word 'convenient' is quoted, since it is not really all that convenient -- this is not a great solution, since it requires effort of the visitor to be able to see your email address. It is recommended that you replace this link with something that is not so labourious for the surfer. You should replace this code in the <noscript> tags to show an image of your email address, instead, so people without JavaScript can at least see your email address without having to change system settings. Note that even in this case, you are requiring extra effort on your visitors.
Usage:
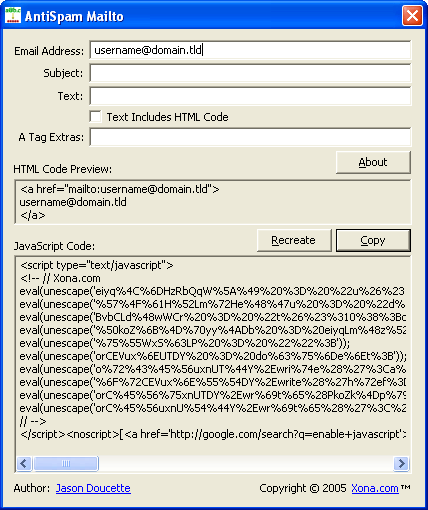
Type in the appropriate information in the text fields. You can view the resultant HTML code that this information produces in real time.
Ensure that the check box 'Text Includes HTML Code' is checked if the Text: field contains HTML code. If this box is not checked, and the Text: field contains HTML code, the HTML code within it will be encrypted as if it were regular text, rendering it useless.
Once all of your information is typed in, press the 'Copy' button to select the resultant JavaScript code and copy it to the clipboard. It will then be ready to be pasted into your webpage. Note that the 'Recreate' button merely recreates a new random encryption, for curiosity’s sake. It is not required, since the final output of the JavaScript code will be the same.
The program accepts command line parameters. The first four parameters will fill the first four text fields, in the order they are displayed. If only one to three parameters are provided, then only the first one to three fields will be initialized.
Download:
Download: AntiSpam Mailto v1.0.5 (91 KB)
No Installation Required:
AntiSpam Mailto does not require installation. It is a stand alone program that runs on its own. It does not write any information to the registry. You do not need to use the 'Add or Remove Programs' selection within the Control Panel to 'uninstall' it, since it doesn't install itself. Just delete the .exe program file if you want to delete it. AntiSpam Mailto requires Windows XP or greater.
Developer:
AntiSpam Mailto was developed by Jason Doucette.
